📣 Create Blog for Traders!
Stop Watching news - Start Making it.
START
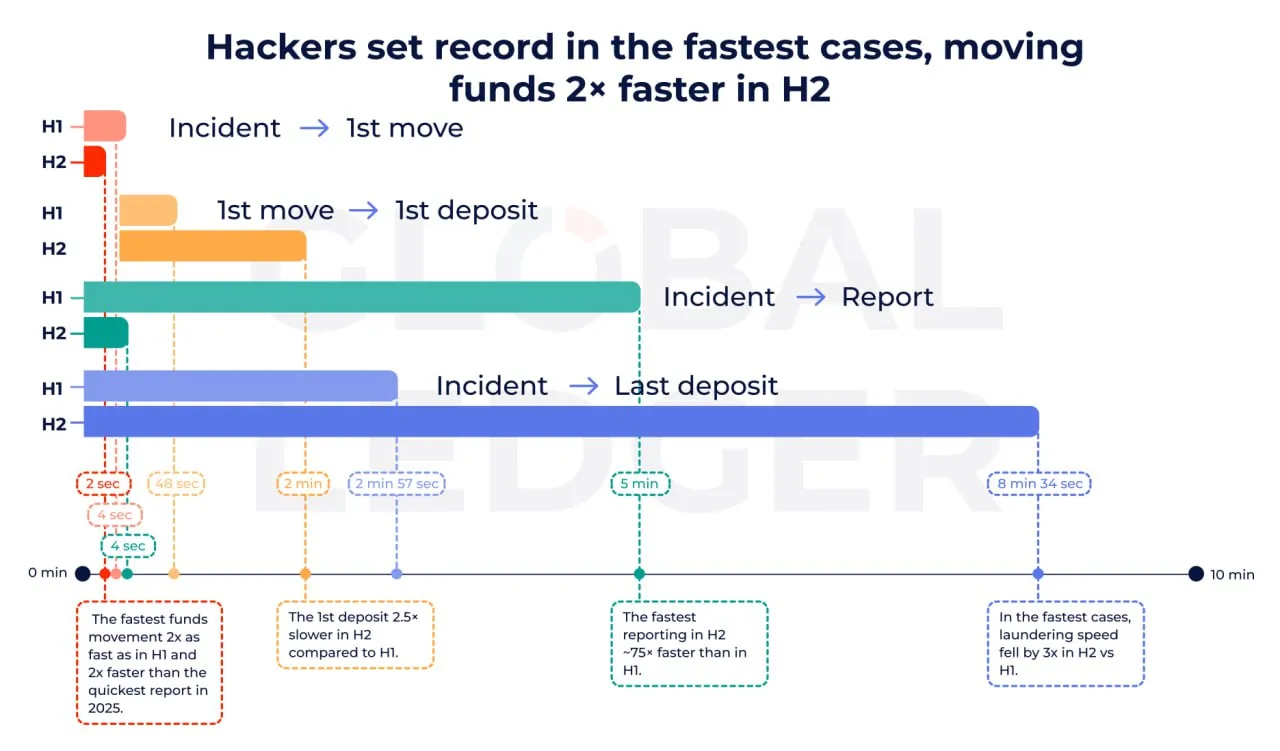
Hackers Move Stolen Crypto in 2 Seconds - Laundering Tactics Evolve

According to a recent industry report, some hackers are now able to move stolen cryptocurrency within just 2 seconds after gaining access to funds.
In 76% of cases, the first outgoing transaction occurs before the incident is publicly disclosed, highlighting how automated and pre-scripted these attacks have become.
🔄 Cross-chain bridges dominate Nearly 50% of stolen funds now pass through cross-chain bridges, making tracking more complex and fragmenting forensic trails.
🏦 Direct exchange cash-outs decline Direct transfers to centralized exchanges have decreased significantly, as attackers avoid immediate KYC exposure.
🧊 Funds left dormant Around 49% of stolen assets remain untouched, likely to reduce tracing risks and wait for investigative attention to fade.
⏳ Full laundering cycle slowing down Despite the instant first transfer, the complete laundering process now takes more than 10 days on average, suggesting attackers are prioritizing stealth over speed.
The shift toward:
- automation
- cross-chain fragmentation
- delayed cash-outs
…signals a more sophisticated threat landscape.
For investors and institutions, this reinforces the importance of:
- real-time monitoring tools
- bridge risk assessment
- counterparty risk management
As crypto adoption grows, so does the operational sophistication of illicit actors.
☠️ #crypto #hacking #onchain #security

